@Tom-Elliott said in Snapin Pack Arguments double-quotes problem:
I’m only guessing here that this was a machine that did not have an image defined to it?
…
I corrected this specifically by setting assocID to null if there’s nothing in the returned assocIDs previously.
Apologies for the long winded answer.
You are correct. The host doesn’t have image associated (as many of our hosts  ).
).
Unfortunately seems with have to dig more…
[Wed Jan 21 14:52:42.687383 2026] [proxy_fcgi:error] [pid 2630261] [client computer_ip:50247] AH01071: Got error 'PHP message: PHP Warning: Attempt to read property "dev" on null in /var/www/html/fog/lib/pages/dashboardpage.class.php on line 586PHP message: PHP Warning: Attempt to read property "rx" on null in /var/www/html/fog/lib/pages/dashboardpage.class.php on line 588PHP message: PHP Warning: Attempt to read property "tx" on null in /var/www/html/fog/lib/pages/dashboardpage.class.php on line 589', referer: https://dev-hostname.it.auth.gr/fog/management/index.php?node=home
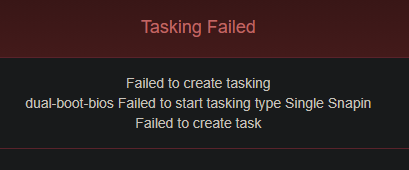
[Wed Jan 21 14:55:03.693789 2026] [proxy_fcgi:error] [pid 2665714] [client computer_ip:57526] AH01071: Got error 'PHP message: PHP Fatal error: Uncaught ValueError: min(): Argument #1 ($value) must contain at least one element in /var/www/html/fog/lib/fog/image.class.php:496\nStack trace:\n#0 /var/www/html/fog/lib/fog/image.class.php(496): min()\n#1 /var/www/html/fog/lib/fog/image.class.php(389): Image->getPrimaryGroup()\n#2 /var/www/html/fog/lib/fog/host.class.php(1133): Image->getStorageGroup()\n#3 /var/www/html/fog/lib/fog/host.class.php(1408): Host->_createTasking()\n#4 /var/www/html/fog/lib/fog/fogpage.class.php(1757): Host->createImagePackage()\n#5 /var/www/html/fog/lib/fog/fogpagemanager.class.php(220): FOGPage->deployPost()\n#6 /var/www/html/fog/management/index.php(69): FOGPageManager->render()\n#7 {main}\n thrown in /var/www/html/fog/lib/fog/image.class.php on line 496', referer: https://dev-hostname.it.auth.gr/fog/management/index.php?node=host&sub=deploy&id=1&type=13
@Tom-Elliott said in Snapin Pack Arguments double-quotes problem:
I corrected this specifically by setting assocID to null if there’s nothing in the returned assocIDs previously.
the imageID in the database is int so maybe the null value causes the error?
FYI I am checking it on the DEV VM (other host without image association).
 Thank you very much!
Thank you very much! 
 ).
).

